“How secure are we?” answered as a grade — not a 400-page report.
ACRE is the institutional security posture answer Boards, CISOs, and engineers can use at the same time. Executive leadership gets a headline grade, narrative, and peer comparison on one page. Engineers see the same finding with asset-level evidence and remediation guidance underneath. No translation layer, no “exec deck vs. technical report” gap where context gets lost.
Generic enterprise attack-surface tools treat every research subdomain as an “exposed asset” because they don't understand higher-ed. ACRE is calibrated for the campus city — your research subdomains, your federated identity surfaces, your decentralized DNS. The scoring rubric is built for institutions, not corporations.
What ACRE evaluates (from outside the walls)
Email authentication
SPF, DKIM, DMARC posture across your domain estate.
TLS / web posture
Certificate hygiene, protocol versions, header configuration.
DNS hygiene
CNAME chain analysis, NS health, subdomain takeover risk — the research-lab-subdomain problem at scale.
Exposed services
What an attacker sees when they look at your perimeter.
Domain and brand
Typosquatting, lookalike domains, brand-impersonation surface.
Asset visibility
Assets attributable to your institution that you may not know about — across schools, departments, and research labs.
Vendor surface
Third-party services in your domain space — the natural feeder for vendor-risk work in Azimuth.
Breach exposure
Credential exposure across known breach corpora.
Policy transparency
Public-facing artifacts that auditors and attackers both read.
Two views, one source of truth
Executive view
A–F headline grade, narrative summary, top findings, peer comparison. One page. Board-ready.
Technical view
Every finding with the asset it applies to, the evidence, the remediation step, and a state machine for tracking resolution.
The higher-ed security landscape today
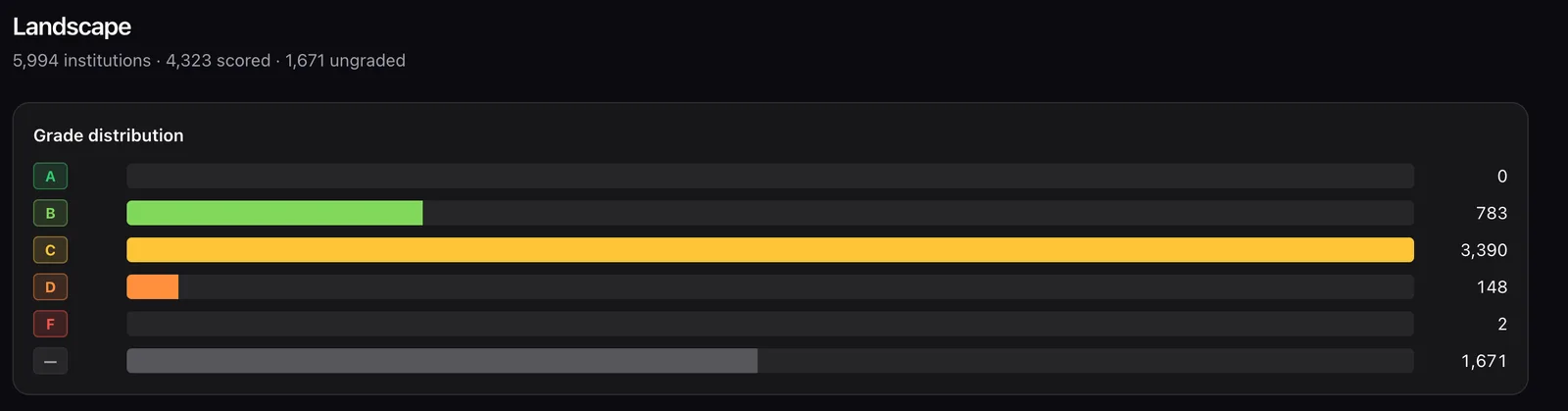
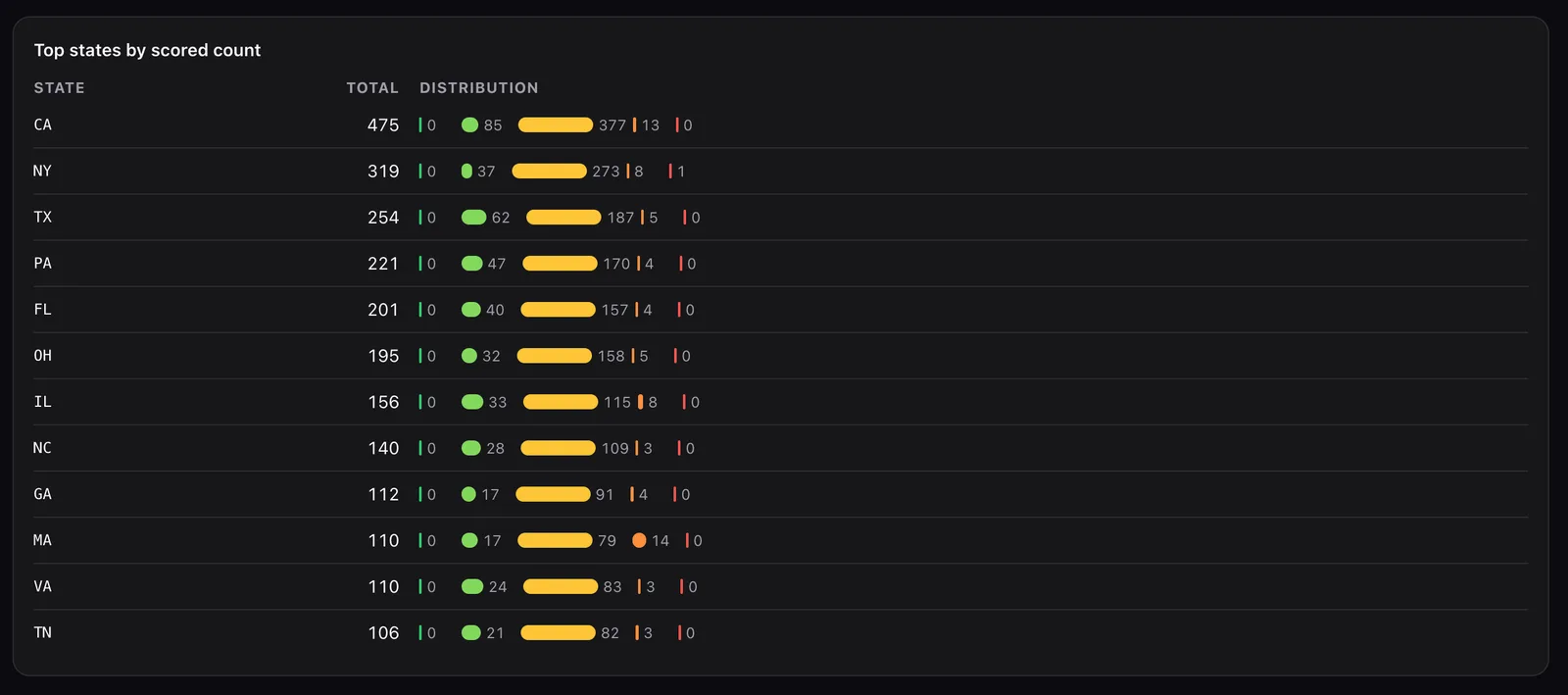
ACRE currently tracks 5,994 higher-ed institutions across the United States with 4,323 scored. Two views from the live aggregate landscape — no individual institution data shown, drill-down is per engagement.
Where it fits the service line
Security Assessments runs ACRE as the engine for the quarterly institutional baseline (we add manual depth on top). Compliance Readiness uses ACRE for the attacker-eye component — each district of the campus city evaluated from outside the walls before the auditor or attacker does it first.
Trust signals
- Observation-only — no internal network access, no credentials, no agents.
- Methodology documented per category so engineering teams can audit every grade.
- Built by Synaptic Cyber practitioners — practicing higher-ed CISO plus decades of higher-ed security architecture experience.
Frequently Asked Questions
- Is this a pentest?
- No — ACRE is observation-only, attacker-eye view. No internal network access, no credentials, no agents.
- Can we compare to peer institutions?
- Yes — anonymized peer benchmarking is built into the executive view.
- How often does it refresh?
- Continuously per category, reported quarterly for Board-cycle alignment.
- Why an A–F grade?
- It's accessible. Boards, faculty, parents, and students all understand letter grades. The per-category subscores give engineers what they need underneath.
- What if we disagree with the grade?
- Methodology is documented per category — drill into the asset-level evidence and tell us where we're wrong. We'd rather get the rubric right than win the argument.
- Can multi-campus systems get rolled-up views?
- Yes — the multi-institution view supports state systems and consortia.
Try ACRE
Sign up at acre.synapticcyber.com to run an initial scan and see your institution's grade. Pricing surfaces in the product once you've seen the value.
Try ACRE →